Featured white papers
The Key To Unlocking K12 School Safety Grants
DownloadPhysical Access Control
DownloadThe 2024 State Of Physical Access Trend Report
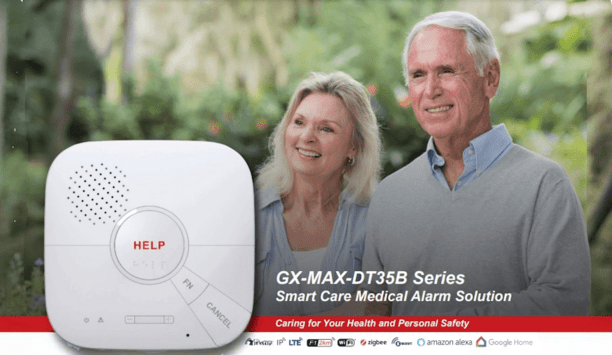
DownloadGuide For HAAS: New Choice Of SMB Security System
DownloadSecurity Practices For Hotels
DownloadThe Security Challenges Of Data Centers
DownloadTotal Cost of Ownership for Video Surveillance
DownloadAccess Control System Planning Phase 2
DownloadAccess Control System Planning Phase 1
DownloadHow To Lower Labor Costs When Installing Video Surveillance
DownloadAre You Ready For An On-Site Emergency?
DownloadUnderstanding Key Control Systems And Best Practices
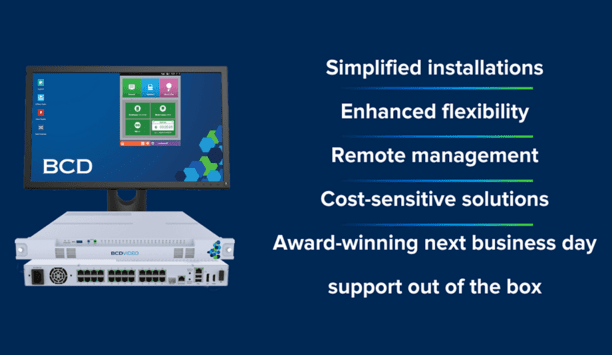
DownloadUnderstanding All-In-One Solutions
DownloadSecuring Data Centers: Varied Technologies And Exacting Demands
DownloadVSS - Top 4 Questions To Get You Started
DownloadSearch for products
Search from our vast range of products (41,041)Featured products
Editor’s picks

Digital access control has well-known benefits over traditional security, of course, but also costs attached to each stage of its lifetime. However, these costs are not fixed. Many factors – inc...

A software platform designed to centralize and manage various physical security systems within an organization used to be called a PSIM (physical security information management) system. Generally speaking, however, the PSIM term has fallen out of favor because the systems were seen as expensive and difficult to manage. The phrase has been replaced by command-and-control, referring to software that combines access control, video surveillance, intrusion detection, and other systems into a unified...

The hospitality industry drives economic growth and development by creating jobs, generating revenue, and initiating a ripple effect to improve profitability throughout the supply chain. The hospitality industry includes a vast number of small businesses, including hotels and restaurants. But what are the security challenges of these businesses, and how is the security marketplace serving those needs? We asked this week's Expert Panel Roundtable: How can technology address the security challenge...

Suddenly, artificial intelligence (AI) is everywhere. The smart technology brings a range of benefits to our lives, from streamlining everyday tasks to making scientific breakthroughs. The advantages of AI and machine learning (ML) also include automating repetitive tasks, analyzing vast amounts of data, and minimizing human error. But how do these benefits apply to the physical security industry, and is there a downside? We asked this week’s Expert Panel Roundtable: What are the benefits,...

Editor
Round table discussions

The security marketplace has its share of buzzwords, which are words or phrases that become popular and widely used in a specific industry. Buzzwords can be useful for conveying complex ideas quickly, but they can also be misused or misunderstood. Within a spe...

By all accounts, technology development is moving at a rapid pace in today's markets, including the physical security industry. However, market uptake of the newest technologies may lag, whether because of a lack of clear communication or not enough education...

Technology automates tasks, streamlines processes, and improves efficiency in various fields, including physical security. But the success of today’s latest technologies depends on our ability to use them responsibly and efficiently. Optimising our indus...
Latest videos
-
 Remote Guarding Video Series Part 1: Overview and Basics.
Remote Guarding Video Series Part 1: Overview and Basics. -
 Remote Guarding Video Series Part 5: Future and Technology
Remote Guarding Video Series Part 5: Future and Technology -
 Remote Guarding Video Series Part 4: Partner to Law Enforcement
Remote Guarding Video Series Part 4: Partner to Law Enforcement -
 Remote Guarding Video Series Part 3: Benefits and High Value
Remote Guarding Video Series Part 3: Benefits and High Value -
 Remote Guarding Video Series Part 2: System Design
Remote Guarding Video Series Part 2: System Design -
 OPTEX REDSCAN Mini Series Protects The Londoner Hotel
OPTEX REDSCAN Mini Series Protects The Londoner Hotel -
 Hofbräuhaus In Munich relies On eCLIQ
Hofbräuhaus In Munich relies On eCLIQ -
 What Alcatel-Lucent OmniVista Network Advisor Can Do For Network Infrastructure
What Alcatel-Lucent OmniVista Network Advisor Can Do For Network Infrastructure -
 Time Challenge: Installation Of Battery Powered Aperio Cylinder
Time Challenge: Installation Of Battery Powered Aperio Cylinder
Case studies

About a year and a half ago, Peter de Jong introduced Dahua to Fred Koks, General Manager of KITT Engineering. Since then, Dahua, KITT Engineering, and Ocean Outdoor have completed five joint projects. Follow-up appointments for the next two projects are already scheduled. Looking back "Let's see what happens" was Fred's reaction when introduced to Dahua. ''We evaluate our portfolio with suppliers every year,'' he explained. "We have to. So much is changing and new technology is developing incredibly fast. You have to keep up." He knows better than anyone how mobile the market is. "Among suppliers of LED screens, there is a constant battle for market position and new technology. We all know the big providers and the market pioneers. But it is not necessarily that they are also at the forefront of technology." Working in collaboration Erwin van Domselaar, Operations & Project Manager at Ocean Outdoor, says his company dares to blindly trust the expertise of Koks and his people when choosing a particular type of LED screen. "KITT Engineering is our technical supplier. They are very good at distinguishing good products from bad ones, and we trust them completely. When they have a product they see a future in, they discuss it with us to see if we can take on a project together with it." Shopping centre - Koperwiek In Dahua's case, that first project is a screen in a shopping center called Koperwiek – an indoor shopping center with more than a hundred fashion-related shops – located in Capelle aan den Ijssel. "That was a relatively small project," Erwin recalls. "The screen was not too big. But the initial learnings and experience with the screen were very good before we started. And the installation itself went off without a hitch. Exactly what we expected from this product." Shopping centre - Sterrenburg Soon, a second project was launched. This time in a shopping center called Sterrenburg in Dordrecht. "Here, not everything went smoothly right away. Not regarding the screen, but its coincidence with the shopping center's renovation. They had just finished." "All the walls had been neatly plastered and at that moment we asked if a new cable could be drawn. Fortunately, all this was eventually dealt with and solved in a very pleasant cooperation with the project developer, but it took some time." Pure craftsmanship The third and fourth projects are true masterpieces. In Hoofddorp, KITT Engineering installed a corner screen. "A unique screen for us," says Erwin. "It is the first screen that goes around a corner. It is half a meter that goes around the corner, fitting in super nicely with the surroundings." "On paper, a huge screen of forty square meters, but when you stand there, you don't notice it because it blends in so well with the surroundings. We are always looking for something new and surprising. And a screen that turns around the corner offers a lot of new possibilities. For example, in terms of 3D content." The screen turns around the corner Fred adds, "The screen doesn't just go around the corner, it goes around the corner seamlessly. KITT is always trying to bring novelties forward so we've had corner screens before. But that was in art projects and things like that where requirements are a lot lower." "In the process, we were able to try out various techniques and we also found out that the products we had at our disposal at that time were not one hundred percent ready." Cold corner "Then Dahua came up with a prototype, we were very pleased with the 'cold corner' as we call it. It is LED on LED, without a seam." To understand how clever this feat of engineering is, it's worth realizing that the margin you have to make the image seamless is the space between two LEDs. Millimeter work, on a length of ten by five meters. Zuidplein shopping centre "The fourth project was placing a screen in the atrium of Zuidplein shopping center in Rotterdam," Peter says. "The screen was placed against a glass elevator." "When you see that, [it is] not normal the way it came together. You don't see a cable or anything. Fantastic." Westfield Mall The fifth project collaboration between Dahua, KITT Engineering, and Ocean Outdoor is an LED display screen in Westfield Mall in the Netherlands. 24/7 remote system monitoring In addition to the regular LED screen and the driving system, a screen control and monitoring system was also developed to monitor the primary system at every point. “We want to see remotely how our assets in the country are doing," Fred explains. From the video player to dysfunctional LEDs, everything can be monitored remotely. For instance, it prevents the light intensity from being too high. Something that can have major consequences in outdoor advertising.
Read moreCompany in profile
Increase your online visibility and get found by relevant security professionals.